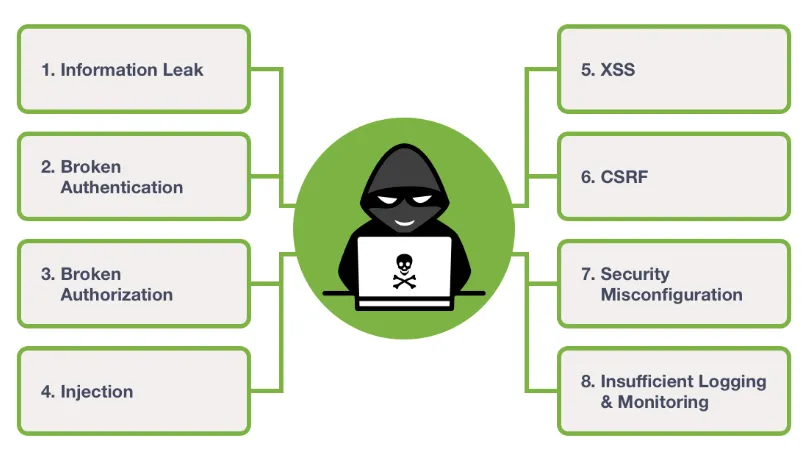
Web Application Security Vulnerabilities

In today’s world, Security is the most crucial aspect especially when it comes to banking or financial applications to prevent disclosure of their sensitive data, malware attacks, interruptions in business continuity, financial loss etc. Most of the times, the security is taken into consideration during testing phase when penetration testing exposes the vulnerabilities in the application. However security practices should be implemented throughout the SDLC so as to reduce additional efforts required to refactor the application to incorporate security measures afterwards.
Web Application security comprises the security of Application Server, Backend Application, Web Application, Database and other external services. In this article, we will cover topmost security vulnerabilities.
Security Vulnerabilities
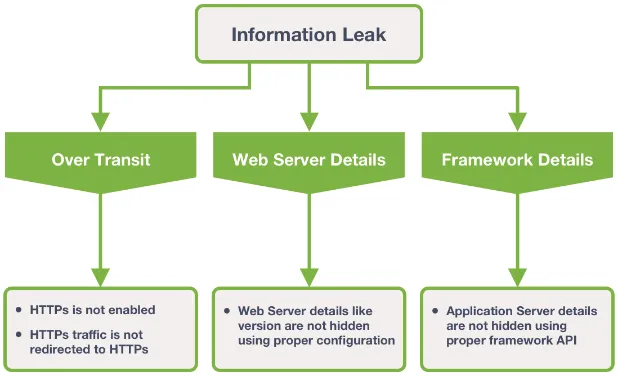
1. Information Leak
Missing configurations in Web Server and Application framework can cause information leak in transit as well as in the API response. Details like web server version, framework used are exposed by default in the response headers and version specific security holes can be utilized to perform version / framework specific attacks.
2. Broken Authentication
Broken Authentication refers to gaining access to user’s account by impersonating the user or hijacking the session. This can be categorized mainly into weak credential management and weak session management.
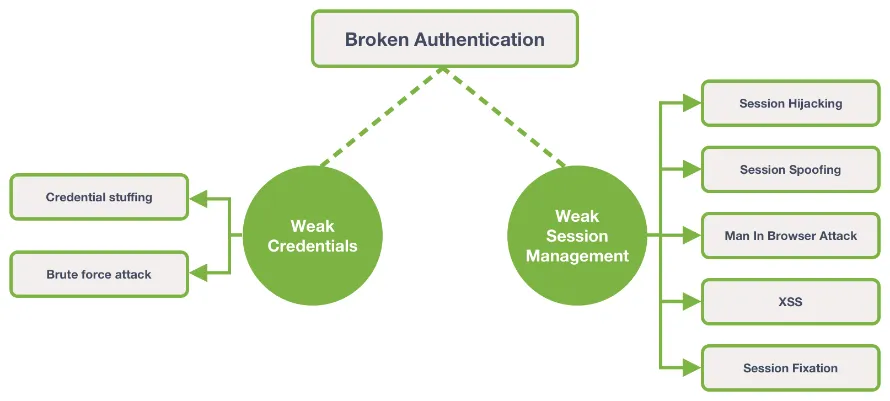
Weak Credentials attack techniques
- Credential stuffing – Steal password from password dump or breached database of one website and attempt to use it on other websites for same user.
- Brute force attack - Guess the password on trial-and-error basis and try to gain access using script / hijacking app.
Weak session management attack techniques
- Session hijacking - Obtain victim’s authenticated session ID by network sniffing and gain control of user session.
- Session Spoofing – Impersonate victim’s session by predicting session ID pattern or bruit forcing session ID
- Man In browser attack – Infect victim’s machine with malware and modify victim’s transaction unknowingly.
- Cross Site Scripting (XSS) - Inject malicious script and read authenticated session ID from Cookie.
- Session Fixation - Use victim’s pre-authentication session ID to perform authenticated transactions on his behalf.
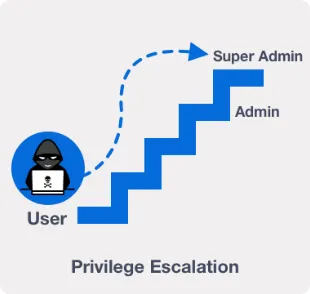
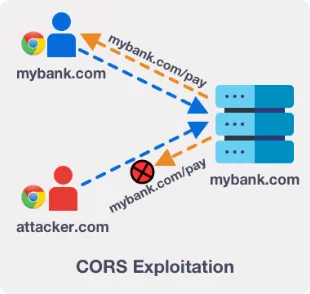
3. Broken Authorization
Broken Authorization refers to exploitation of access control across horizontal and vertical privileges. With the lack of proper Authorization control, users can perform actions outside their intended privileges.
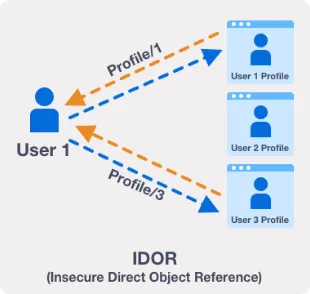
- Insecure Direct Object Reference (IDOR) – Objects can be accessed directly by modifying user supplied inputs. For example, just by modifying organizationId in the url, Admin is able to fetch user information of another organization.
- Privilege Escalations – With this, user is able to perform actions that he has not privileges for. For example, normal user can perform actions that only Admin is privileged to perform.
- Exploiting CORS – In case of incorrect CORS configuration i.e. returning user’s origin as Allowed-Origin, attacker can call APIs on behalf of victim and can exploit his data.
4. Injection
Injection refers to injecting code / script via user input in the form of request that can exploit backend resources or execute given command.
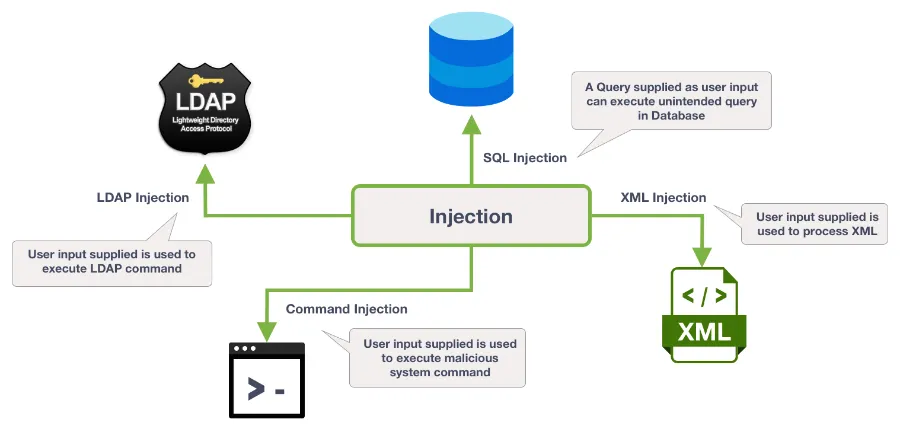
- SQL Injection – Inject partial or complete query into the application via user input that can expose / modify / delete data from Database.
- LDAP Injection – Inject user input to expose / modify / delete data from LDAP.
- XML Injection - Inject XML input that may corrupt XML document causing XML processing failure
- Command Injection - Inject system command that executes to expose sensitive data or corrupt the system files
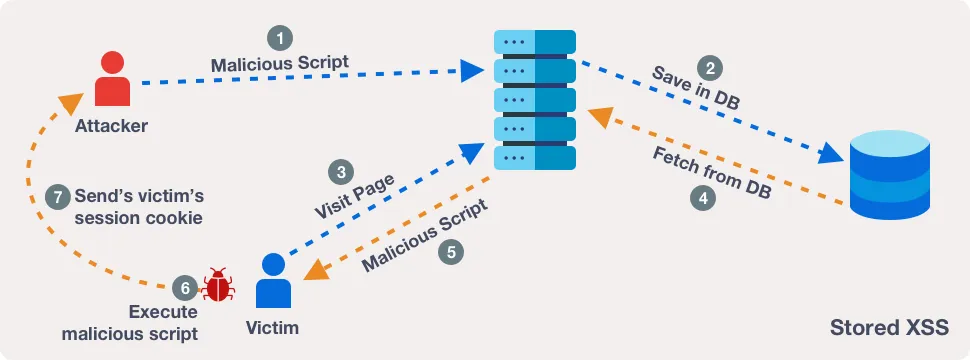
5. Cross Site Scripting – XSS
Cross Site scripting refers to injecting malicious scripts so as to compromise user experience or to hijack user’s session.
-
Stored XSS - Application receives the malicious data from
request but is returned in unsafe way in later http response.
Example: A blog post may contain malicious script which can compromise the user experience when victim visits the website. -
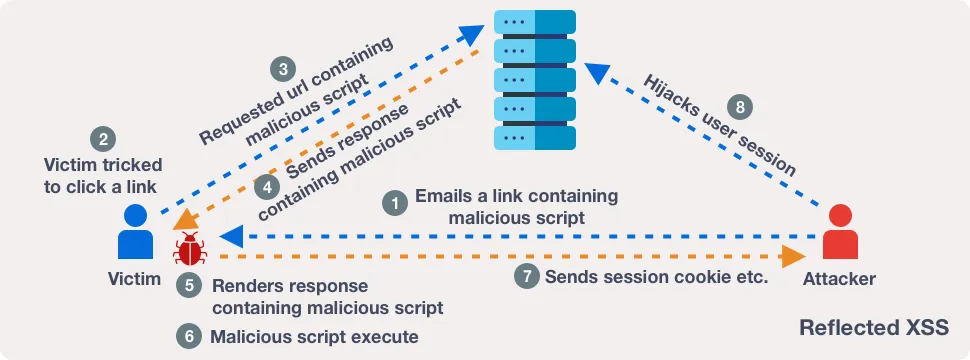
Reflected XSS – Application receives the malicious data from the
request and is immediately returned back in the response in an
unsafe way. This malicious data is reflected back on the page.
Example:https://insecure-website.com/welcome?name=<span>alert(“hi”)</span>
Welcome: alert(“hi”)
-
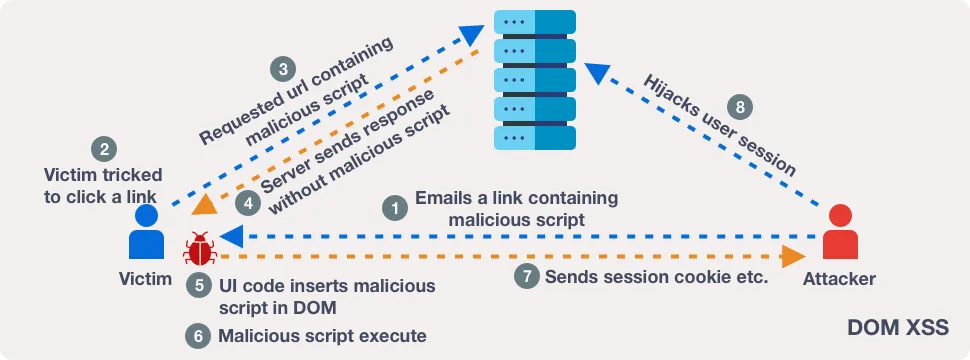
DOM based XSS – This arises in client side javascript code when
data received from untrusted source is processed in unsafe way,
by writing the unsafe data back to DOM.
Example:var = document.getElementById( ‘searchInput ‘ ).value;
var = document.getElementById( ‘searchResults’ );
searchResults.innerHTML = ‘You searched for: ‘ + searchInput;
You searched for: src ”xyz” onerror ‘while(true){alert(“hi”)}’
6. Cross Site Request Forgery – CSRF
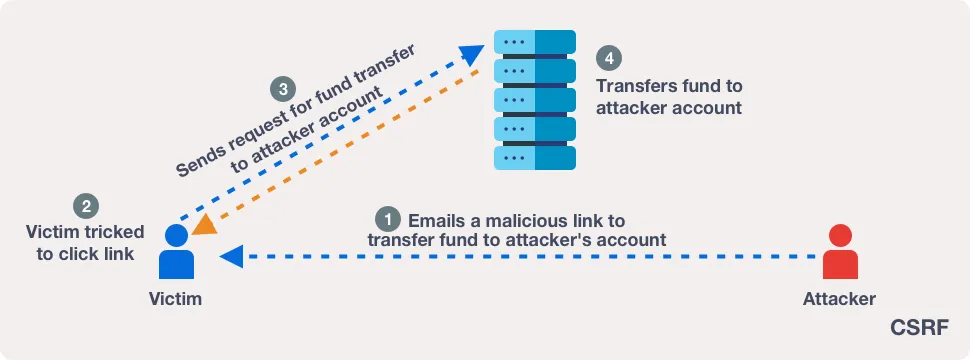
In CSRF, attacker tricks the victim to click on evil link and secretly sends malicious request to application server to perform unintended action like transferring money from victim’s account to attacker’s account. The CSRF attack is possible when browser is automatically providing authentication information to your request like cookie / bearer token. If you are using a custom token in header for authentication, CSRF attack is unlikely to happen.
7. Security misconfiguration – CSRF
Security misconfigurations leads to back door open for attackers due
to some misconfiguration on Application server, deployment
environment, libraries etc.
Examples of misconfigurations –
- Proper access privileges are not applied to files/directories causing directory traversal.
- Default, temporary, or guest accounts are not deleted from the Webserver.
- Legacy third party libraries are used without checking security vulnerabilities.
8. Insufficient Logging and Monitoring
Insufficient logging and poor monitoring causes issues like -
- Give a chance to attacker to perform certain attacks repeatedly.
- Makes it difficult for developers to debug and fix the issue.
- In rare cases, makes it difficult to track the individual when it comes to legality.
With in-efficient exception handling, complete stack trace is displayed to the user disclosing additional information which attacker can use to identify vulnerability.
Hence we covered major security vulnerabilities and will cover security measures in upcoming Article!